The notion that Cybercrime is fueling the Cryptocurrency market through money laundering activity-they are interdependent. If we eliminated 95 percent of cybercrime, we could declare victory and keep $5 trillion moving in our global economy.
I picked today to start writing because Bitcoin mining rewards halves today. BTC halving simply means a 50 percent pay cut for building (mining) block chains, therefore, I cut my expenses by half resulting in 50 percent less blocks verified per period-advantage cybercriminal. When I wrote the part one article, BTC was trading at $6,800. This past Friday it closed at $10,000. No one can predict if the BTC mining cutback is going to affect the coin price as it has in the past. I believe it will go up because of the COVID-19 pandemic and ignore the 50 percent mining reward cut. Hackers are having a field day with us opening our systems to enable work from home, and this summer we will see an uptick in reported cybercrime. Hackers will have more money to push into BTC. BTC market cap will grow, and that is the fuel for BTC appreciation.
Three promising approaches core to our perimeter defense doctrine are coming on-line and will become game changers in stopping cybercrime: Identity and Access Management, Software Defined Perimeter, and Searchable Symmetrical Encryption. Think about what’s important-people accessing content-it’s that simple.

Identity Management has many implementations today, but the trend is to cloud solutions because of the resources they can touch and the vendor community can support-Cloud IAM. Single Sign On (SSO) was one of the first tools and even though it helped, it had limited utility and IT remained with multiple silos to management. Users, in general, need more for online safety as they work, shop, bank, travel, and more. There are already certain restrictions in place for those who want to access casino sites, hence why are so many are looking into how to bypass roobet location checkpoint, for example, to ensure they have the opportunity to play the games on this site. This type of protection is something that should be in place for all sites. Also, the point is Identity Authentication is paramount for the individual, the people and the organizations around them. Supporting one identity provider has many benefits for all concerned. Users could interface with one site for all their online needs including work. These identity providers offer Multifactor Authentication (MFA) features like fingerprint scans, facial recognition, GPS location, IP address, behavior analytics and complete isolation when bad actors are detected. What if an online store hack of an individual could close their ability to access company assets, or a company hack could lock down all your employees’ bank or credit card accounts?
The workplace now can rely on one access integration point and enhance their users’ experience. Vendors now can set requirements with the identity provider on the type or level of authentication required (i.e., password greater than eight characters, two-factor, bio rec, etc.) before granting access. A unified access portal where users can set vacation flags turning off work access but opening travel destination access. Wallet security questions further personalizing the individual identity. This process could help adoption for electronic signatures, video conferencing, voting, law enforcement and electronic health records. Users could get their own access reports, and all concerned could be notified when an alert is triggered or a distress condition is set.
Validating and testing the identity are also important. Individuals have a responsibility to validate their identity by an onboarding process where nonpublic information is asked, and answers provided much like the experience of locking down your credit reports at TransUnion, Equifax, and Experian. Then an annual recertification process to ensure all the information and goals are being met.
The Cloud IAM market is taking shape with the usual suspects, Google (Cloud IAM), Amazon (AWS IAM) and Microsoft (Azure AD). There are many IAM vendors in the market, the first started around 2007 focused on company enterprise solutions benefiting the company not the individual. Cloud IAM vendors are focused on both the individual and the company enterprise. Leverage the reach of the cloud to ensure access security and stop the decentralized landscape we endure today-fifty different points of potential failure deployed by fifty different companies. Hackers rarely waste time with companies that deploy MFA solutions because there are so many who have not. Today, you are best served to extend your password length to 10 or 12 characters or use passphrases, enable two factor authentication and IP restrictions.
The second change of behavior comes from the Cloud Security Alliance Association (CSA) known as the Software Defined Perimeter (SDP). The Software Defined Perimeter solution is designed to stop network attacks against application infrastructure. With the adoption of cloud services, the threat of network attacks against application infrastructure increases since servers cannot be protected with traditional perimeter defense techniques. The traditional fixed perimeter model is rapidly becoming obsolete because of internal security neglect or bad actors, BYOD that attach to internal networks, phishing attacks and IoT devices that introduce malware providing untrusted access inside the perimeter-the classic Trojan Horse.
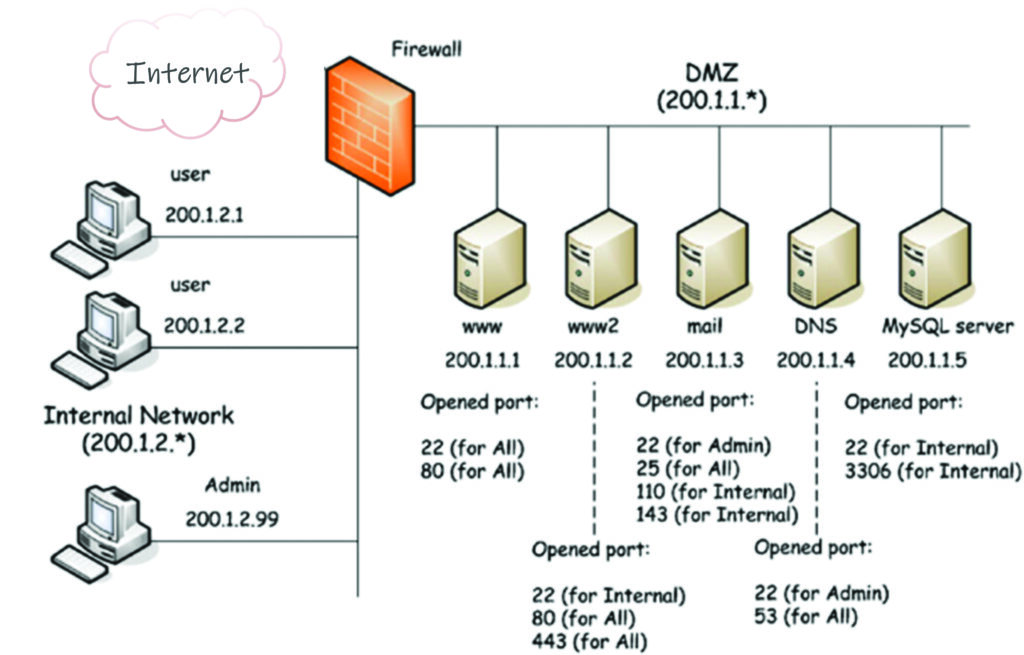
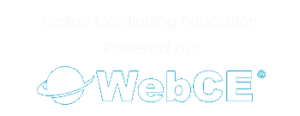
Connectivity in an SDP is based on a “need-to-know” model, in which device posture and identity are verified before access to the application infrastructure is granted. Today’s perimeter approach is too broad when looked at from underneath (what I call the plumbing). Vendors building SaaS solutions design three layers separated by firewalls and connected via VPNs and NACs. Unfortunately, what is in view across the network can be seen if you know what you are looking for-hacking. CSA states this as “Authenticated users have overly-broad network access, increasing the attack surface area and enabling the types of wide-reaching breaches that we see far too often.”
Let me give you this example: You are kidnapped and being driven to a secret location, all the while watching the scenery and sites as you travel. SDP environment is the same story but this time they blindfold you going to the secret location. The Department of Defense and Intelligence community call this a “Black Network.” In effect, SDP establishes a direct connection from you to the host resource (application) you are requesting and if the host resource needs help from a different host resource (database) a new connection is created between host resources only. The SDP instrument managing all these connections is called “SDP Host Controller.” Now that I’ve over simplified SDP, the concept is, there is no plumbing-connections are dynamic.
So far, we have discussed Cloud IAM solutions designed to ensure your identity and maintain your authentication. SDP introduces Black Networking where the identity also has a “need to know,” or privilege to a portal or application. The bad guys now have a tremendous challenge to break in from the outside. Eight-character passwords are considered weak security when that is the only challenge separating the bad guys from your third-party trusted content. With cybercrime growing 15 percent per annum, our security perimeter needs to change. Bad guys are smart too. The technique of brute force password hacking is seldom used because it is much easier to be invited in. Phishing, URL Forgeries, and Social Media Impersonations are just some of the techniques used whereby one click is all they need. Then they sneak in some Java code infecting File Explorer, coming to life the next time you start File Explorer. Red Flag: If your File Explorer starts doing odd things (i.e., very slow, chopped screens, bad characters) then you should sweep your device in Safe Mode with a capable commercial tool.
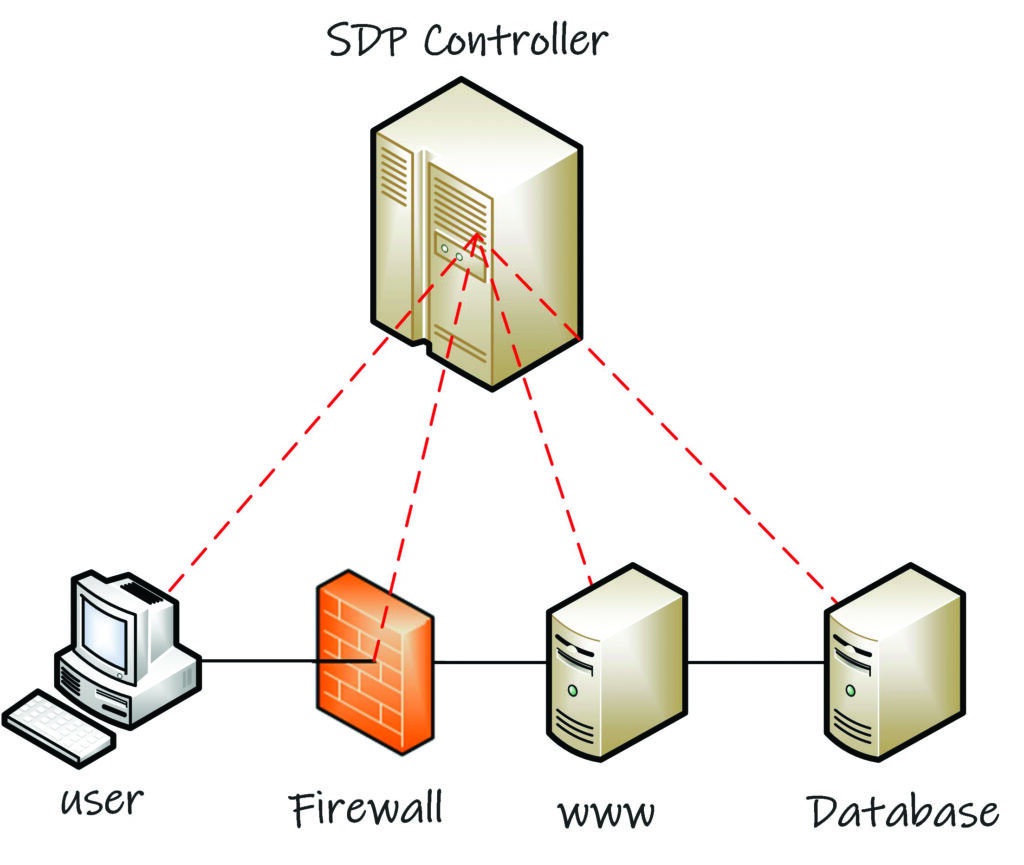
What can we do when the bad guys gain access inside our defenses…eliminate their reward? Yes. We want an ending like Geraldo Rivera opening Al Capone’s vault-nothing. Well that goal has been long coming because today’s database protection is non-existent. Databases are secured by Transparent Data Encryption (TDE) or Cell Encryption (CE). TDE encrypts appropriate database files (every row) and CE encrypts only the field (cell) where the data exist-a column. They both use one symmetrical key, and each has pros and cons.
TDE is good for “Data at Rest,” which means the database is inactive but cannot be reasonably searched because you must decrypt all the rows before the query can begin. According to Matthew McGiffen, “When TDE does not read from disk it doesn’t add any overhead, but how do we quantify what the overhead to queries is when it does have to access the disk? From my testing we could suggest it adds from 10 percent to over 1000 percent CPU.” (Thoughts on Query Performance with TDE enabled, May 23, 2018). To make it clear, it kills performance not just for you but everyone. Microsoft, who created TDE in 2008, now offers Always Encrypted SQL where the data is encrypted at the workstation. This distributed model makes sense-offloading the server-but we want to move away from workstations and the thought of moving symmetrical keys across the enterprise would make any IT organization nervous.
CE is a column level encryption; it encrypts only the sensitive information in a table column. With CE, the data is still encrypted even when searched and decrypted when displayed. Just like TDE though, if you search on that column, then the entire column is decrypted. Again, a performance killer. How much of a killer? A 5,000,000 row database with one encrypted column takes 12 seconds to return results compared to 0.0012 seconds when not encrypted. User mutiny.
The real problem is TDE and CE are not that secure because of the leakage they create. Leakage is a term used to describe breadcrumbs and artifacts left in the SQL database which enables hacking. A great demonstration of this is a 10-minute video published by Simon Mcauliffe (https://simonmcauliffe.com/technology/tde/) where he steals a TDE database and hacks it revealing all its decrypted content. Ten minutes.
In 2005 scholars started a subject called “Searchable Symmetrical Encryption” and many doctoral theses were launched. And that is where it ended-abstracts and a bunch of calculus but no products-until now. I have watched over the last four years our version of SSE perform with virtually no overhead and no leakage; a totally different approach to securing data making it searchable and secure. Security that does not encrypt plaintext data but instead shreds the data with no context. It does not store data in rows but builds algorithms that bring order to shreds of data across multiple records; a mathematical non-equation (equations that produce more than one answer). Hackers rely on seeing encrypted text and plain text together as best portrayed in the war movie Midway (AF). Without these relationships hackers are flying blind. SSE that supports more than one symmetrical key making it impossible to remove (steal) the database. A total scheme that delivers no value to thieves and will not for the next 100 years. As an employee of a company that builds supply chain solutions, my company will not rest until we complete our SSE project, eliminating risk for the data we manage and report that we do not store confidential information.
Cybercrime reached over $5.5 trillion dollars last year. The bad guys cashed out for $1.5 trillion and the victims paid out an additional $4 trillion covering the lost $1.5 trillion and $2.5 trillion in mitigation cost, technology, fines, and lost reputation compounded with departing senior management.
Protecting confidential information from bad guys is obtainable and the above discussed subjects collectively can put hacking in the past. Publishing the fact that XYZ Company has deployed Cloud IAM, Black Networking and Shredded Data at Rest should be more than enough for Bad Guys to move on and not waste their time. Of the three options, Shredded Data Storage would have the least impact on deployment and stop the potential loss of confidential data immediately.
In signing off, BTC is selling at $9,400, no effect from the halving four days ago. And if you are in BTC, sell high-because the party is about to end.