Let’s start with some findings relating to breach and current events. A mega breach is more than a million rows of data lost or stolen. A million records is not hard to get to these days and, if breached, the remediation expense is the heaviest in year one, two-thirds. Year two is 22 percent and then 11 percent for the out years—but experience would tell us that toward the end of an event like this the last 11 percent will cost you about half your money and half your time.
Who’s breaching you? Fifty-one percent are your classic hackers, outsiders, out there to just get some financial gain and steal identities. You can basically divide a breach into three motivated categories: Identities, financial and health. Identities have value for impersonation, people trying to use your ID to get a job, travel and more. Financial theft is all about what it sounds like, taking someone else’s money—steal a credit card and use it until it dies. Medical record theft has the most value, a complete identity kit. The dark web calls this theft “The FullZ,” everything you need to build a new life.
Twenty-four percent of breaches are human error—those are your employees clicking on websites not knowing what they’re doing and downloading malware or getting phished via email. Twenty-five percent of breaches are from system glitches. This one makes me smile because a system glitch is something that breaks but then fixes itself. In software systems, to me, that’s just bad coding and “fixes itself” is when services are restarted or computers are rebooted. Hackers are always looking for bad coding or what we call “vulnerabilities.”
Another important statistic today is the likelihood of being breached. In 2020 you are one-third more likely to get breached in the next two years. If you’re sitting at a table right now with someone to your right and left, you or one of them are going to get breached.
The anatomy of a breach is a collection of events and the time they play into.
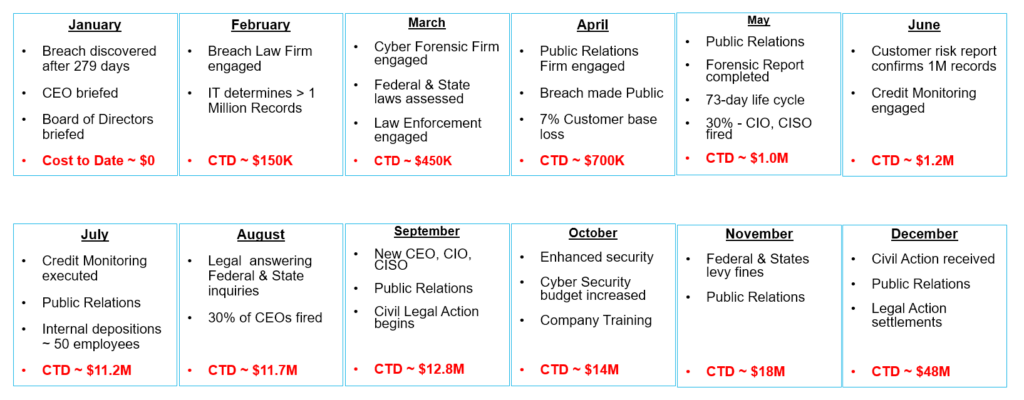
January: For the last 279 days on average the hackers have been sitting in your system undetected. They have figured it out through elevated access, privileges, passwords, and discovery—for almost nine-plus months. They now have all your data and now you just discovered it! Equifax hackers sat in their systems for ninety days until they were discovered. The CEO is briefed, the board of directors are briefed, everybody pulls out the playbook or the incident plan, and hopefully everyone has one so they can determine the next play to call.
February: Well that is obviously to go to your breach law firm—every organization should have a law firm with breach experience. I mean, through contracts or any type of cyber questionnaires or surveys about breach notices, the lawyers are running the show. Do not think your employees will be calling customers telling them that they just got breached and lost all your NPI, PII and PHI. The law firm is going to manage communications. Your job is to start determining how many records are stolen, isolate the vulnerability and plug up the hole.
March: The law firm has now picked a cyber forensic firm. They’re working very hard collecting information, interviewing your IT and other individuals concerned. Other people in the firm are researching and assessing federal and state laws. They’re trying to understand what the level of breach is and whether there are any safe harbor exemptions. Then the next decision is how and when to contact law enforcement if they didn’t call you first. Many times a company first hears of the breach when law enforcement calls them because they found data related to you.
April: Public relations firm is now selected; somebody has to go out and tell the world that this breach event has happened. So, they are being coached by the law firm, and forensics firm, and everyone agrees when to go public. It now tracks pretty well that seven percent of your customer base is lost—and that means they’re not coming back.
May: In May, public relations is fully engaged, the forensic reports are coming in and you now know the who, what, when and where about the breach. Full knowledge of the breach, on average, takes 73 days. Once all that information comes in, 30 percent of those breached companies fire the CIO or CISO.
June: With all the reports coming in you now have identifiable, quantifiable records to address. The company, the law firm and the PR firm gather and decide on what credit monitoring to engage. It is very clear now what the state and federal laws are that must be adhered to.
July: Credit monitoring selected is directly related to the information stolen. Identities are going to cost you about 10 to 15 dollars…if that included financial information you’re getting up there around fifty bucks…and if that also included medical information then you’re nipping at a hundred dollars per record. So this is where the big money starts to spend; now you’ve spent ten million dollars just to go out and protect people’s credit for a year. And just so you know, the average shelf life of people’s data is four years. Back at the ranch the law firm is talking to your employees involved that may have any information that could help. The real critical part of this is that they are looking for the decision of negligence, a breach of duty, because a finding of gross neglect down the road here is going to be a multiplier for what’s coming.
August: The law firm is now answering all the federal and state inquiries. They know what they must report—to whom and by when—while starting those interviews. Now the board of directors have decided if the CEO stays or goes. Three out of 10 CEOs are terminated.
September: When the Board reaches decisions like that, they’ve pretty well figured out who they’re going to hire. The interesting thing here with the new CEO, CIO or CISO, they’re looking for people, oddly enough, who have breach experience—experience that will help them navigate over the next few years. Public relations remain engaged, they’re running with the company message, working its reputation, getting out there as much positive information and truthful information as they can. Now all the people who are going to be hurt and become victims form up and start bringing civil actions.
October: The new CEO and team have decided on what enhanced security they want to deploy immediately, they promised to increase the cyber budget by two or three times, and everybody in the company has to go through cyber training multiple times.
November: The federal and state fines are being levied, you know how much they want, and a lot of it is being driven again by the type of information that was taken. Equifax has paid over $700 million dollars in federal and state fines. Public relations is continuing their work.
December: The legal group continues the civil actions; public relations continues working and settlements are being agreed upon. Your one million record data breach has cost you now $48 million dollars. Two-thirds, so as you can see when you start taking that out over the next couple years you will be nipping at $100 million dollars.
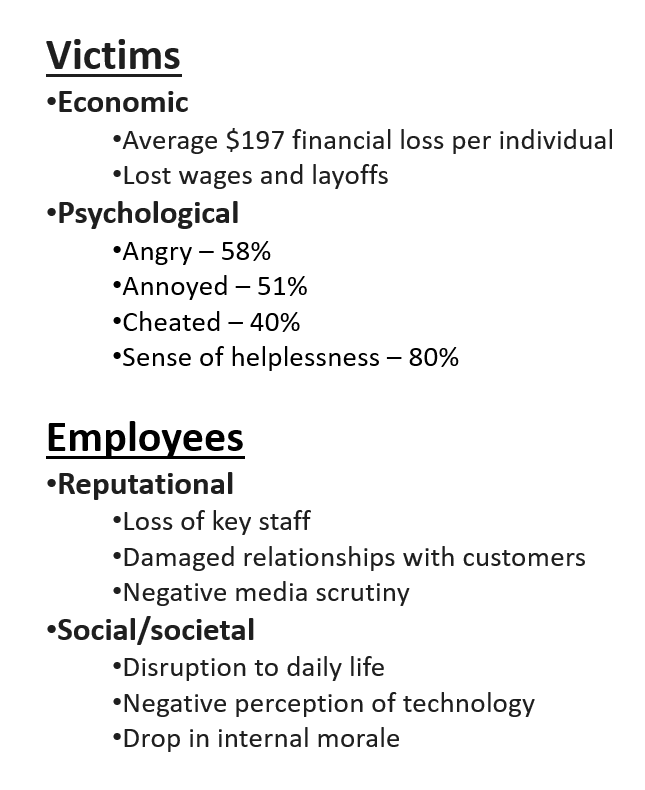
Let’s turn the conversation now to the people whose data, that you were entrusted to protect, have been affected. The average victim is losing $197 dollars. If they are a casualty of this breach, they could lose their job or contracts through no fault of their own.
The psychological effects of anger, annoyance, being cheated and, as you can see, most everybody just has a sense of helplessness. What is interesting here is that cyber-crime today in 2020 is tracking with what we’ll call physical crime—assaults and burglaries. People have that same emotional stress now about their electronic records as they do about their property.
Back at the shop employees have reputational issues, you have already lost some of your key members, and soon other staff will be lost. Those that work with the customers constantly having to defend and promise that they can and will do better. The media is nothing but negative press. You lost customers’ data. How dare you lose their data!

Social media is just a disruption and the people get a negative perception of technology; when someone really wants to come out and tout something new people just see it as another chance to be robbed. Morale, for obvious reasons, has reached a low point and that’s where the leadership has to come in—positive action and positive leadership.
Economically $197 dollars doesn’t sound like a lot, but when you take it times a million that’s a $197 million dollars that’s coming out of the people that trusted you to protect their information. And some of them will never be made whole. Example: In the 2020 settlement for Equifax, the court capped the top line claim to $20,000. If you lost $30,000, or $50,000, you lost money and you are not getting it back.
Of course with all these individuals and the way they feel, 80 percent of them said they will continue to use the internet despite the risk—so they will just become victims again when the next group gets hacked. Equifax lost control of 150 million records consisting of identities and financial information, almost half of Americans. To date, Equifax has paid out over $1.3 billion dollars.